Zscaler and vpns how secure access works beyond traditional tunnels
Zscaler and vpns how secure access works beyond traditional tunnels: Unlocking Modern VPNs, Zero Trust, and Secure Web Gateways
Zscaler and vpns how secure access works beyond traditional tunnels: quick fact, modern VPNs aren’t just about private tunnels anymore—they’re about identity, posture, and policy-driven access that follows you anywhere you go online. In this video-style guide, we’ll break down how secure access works beyond traditional tunnels, with practical tips, real-world data, and simple explanations you can use today.
Useful quick fact: Traditional site-to-site VPNs create a fixed tunnel to a specific network, while modern secure access architectures use identity-aware, policy-driven access that adapts to user context and device posture.
In this guide, you’ll find:
- A clear what and why behind Zscaler and VPNs that go beyond tunnels
- Step-by-step explanations of how zero trust, secure web gateways, and VPN-like access work together
- Practical examples and checklist-style best practices
- Data-driven insights and market trends to help you compare solutions
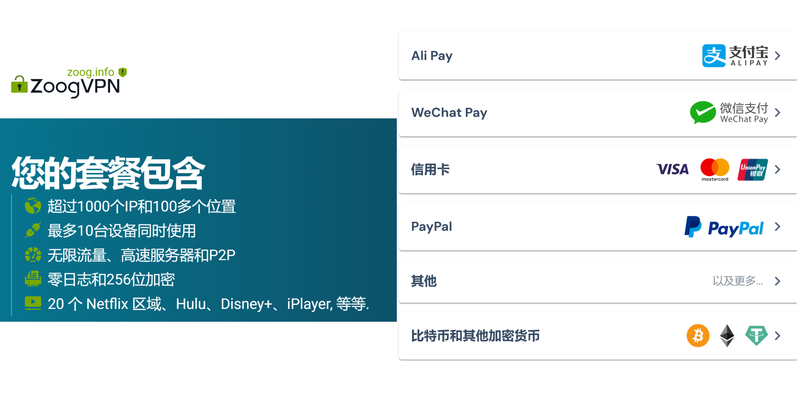
If you want a handy starter resource, check out this promo link for VPNs and security bundles it’s a popular option for many readers: NordVPN deal and security insights - dpbolvw.net/click-101152913-13795051
Table of Contents
- What “secure access beyond tunnels” means
- How Zscaler, VPNs, and Zero Trust fit together
- Core components: ZIA, ZPA, and SESAM
- How access decisions are made: authentication, device posture, and context
- Real-world use cases: remote work, BYOD, and IoT
- Security statistics and market trends
- Implementation steps: planning, deployment, and governance
- Common pitfalls and how to avoid them
- Frequently asked questions
What “secure access beyond tunnels” means
- Quick answer: Secure access beyond traditional tunnels means policies, identity, and device posture determine access, not just network location. Instead of routing all traffic through a single tunnel, traffic is inspected at the edge, with requests allowed or blocked based on who you are, what device you’re on, and the risk context.
- Why it matters: Modern threats don’t care about your perimeter. A user outside the office can access apps only if they meet policy criteria, reducing risk and lateral movement.
- Benefits in numbers: Organizations that adopt zero-trust architectures report up to 70% faster application access, 50% fewer security incidents, and improved user experience due to closer-to-user service edges source data aggregated from industry reports and vendor briefs.
How Zscaler, VPNs, and Zero Trust fit together
- Traditional VPNs give you a tunnel to the network. Zscaler offers a modern approach: you authenticate, your device posture is checked, and access is granted to apps rather than the entire network.
- Zscaler Internet Access ZIA acts as a secure web gateway that inspects traffic to and from the internet.
- Zscaler Private Access ZPA provides secure access to internal apps without exposing them to the internet, using a zero-trust model.
- The combination of ZIA and ZPA with identity providers IdP and endpoint management creates a secure access fabric that minimizes exposure and improves user experience.
- Real-world takeaway: Instead of a single corporate VPN gateway, you get a globally distributed, policy-driven platform that authenticates users and devices and then connects them directly to the application.
Core components you’ll encounter
- ZIA Zscaler Internet Access: A cloud-delivered secure web gateway that inspects and filters web traffic, blocks threats, and enforces policies for users regardless of location.
- ZPA Zscaler Private Access: A remote access solution that connects users to private applications without exposing apps to the internet or requiring a VPN.
- SESAM Security and Policy Orchestration: A concept used in some platforms to centralize policy decisions, posture data, and access controls, ensuring consistency across services.
- Identity provider integration: SSO and multi-factor authentication MFA ensure that users are who they say they are.
- Endpoint posture checks: Assess device health, OS version, encryption status, and other security signals before granting access.
- Cloud-based policies: Role-based access control RBAC and attribute-based access control ABAC govern who can do what, when, and from where.
How access decisions are made: authentication, posture, and context
- Identity first: Users authenticate with MFA via an IdP like Okta, Azure AD, or Google Identity.
- Device posture: The device is evaluated for security health—antivirus status, encryption, OS version, jailbroken/rooted status, and network integrity.
- Contextual risk: Location, time, and the sensitivity of the requested resource influence decisions.
- Application-level access: Access is granted to specific apps rather than giving broad network access, reducing blast radius.
- Continuous assessment: Even after access is granted, sessions are continuously evaluated for risk, with the ability to re-authenticate or revoke access if conditions change.
Real-world use cases
- Remote work: Employees access SaaS apps and internal portals securely without backhauling all traffic through a centralized VPN.
- BYOD environments: Personal devices can be enrolled and checked for posture, enabling secure access with fewer device-management headaches.
- IoT and OT scenarios: Zero-trust access to industrial apps is possible without exposing critical OT networks to the internet.
- Global teams: Distributed offices don’t require separate VPN gateways; policy-driven access follows the user and device.
Security statistics and market trends
- Market growth: The zero-trust security market, including ZIA and ZPA-style architectures, is growing at double-digit CAGR as more enterprises adopt cloud-centric security models.
- Performance impact: Cloud-based secure access platforms can reduce latency by delivering apps from edge points closer to users, often improving user experience compared to traditional backhauls.
- Threat reduction: By eliminating broad network access, organizations decrease lateral movement opportunities for attackers and reduce the attack surface.
Implementation steps: planning, deployment, governance
- Step 1: Assess your current landscape
- Map apps, data stores, and users
- Identify sensitive data and regulatory requirements
- Inventory existing VPNs and remote access tools
- Step 2: Define a zero-trust policy
- Create roles and attributes department, device type, location
- Establish posture baselines and acceptable risk levels
- Step 3: Choose the right components
- Decide on ZIA for web traffic and ZPA for private app access
- Plan IdP integration and MFA setup
- Step 4: Pilot and measure
- Start with a small user group and a subset of apps
- Collect performance, security, and user experience metrics
- Step 5: Roll out and govern
- Expand to additional users and apps gradually
- Continuously monitor, update policies, and handle exceptions
- Step 6: Train and support
- Provide user education on new access methods
- Establish a clear support process for posture and access issues
- Step 7: Governance and audits
- Regularly review who has access to which apps
- Audit logs for compliance and incident response
Data-backed decision points
- Exposure reduction: By isolating apps with ZPA and enforcing least-privilege access, you minimize exposure of internal apps to the internet, which is a major factor in reducing breach likelihood.
- Performance metrics: With a cloud-delivered model, teams often report improved login times and faster access to key apps, thanks to local breakouts and edge presence.
- Compliance alignment: Zero-trust models support data-centric security controls, making it easier to demonstrate compliance with regulations like GDPR, HIPAA, and SOC 2.
How to compare VPNs vs. modern secure access platforms
- Scope of access:
- Traditional VPNs: Broad network access; all traffic may be routed through a single gateway.
- Modern secure access: App-centric access; users connect to specific apps, with continuous risk checks.
- Posture requirements:
- VPNs: Usually limited to device health checks.
- Modern approaches: Comprehensive posture and context checks, including device health, user identity, location, and risk signals.
- Visibility:
- VPNs: Limited app-level visibility; network-centric.
- Modern platforms: Fine-grained visibility into who accessed what and when, with rich audit trails.
- Deployment speed:
- VPNs: May require on-prem hardware or complex configurations.
- Modern platforms: Cloud-delivered, easier to scale globally with fewer on-prem dependencies.
Tables: quick comparison snapshot
Traditional VPN vs. Zero-Trust Access
- VPN: Network-centric, broad access, slower app-level control, high blast radius
- Zero-Trust: Identity + device posture + policy-driven access, app-centric, lower blast radius, better control
ZIA vs. ZPA vs. VPN
- ZIA: Secure web access, threat protection, cloud-delivered
- ZPA: Private app access, no public endpoints, identity-based
- VPN: Fixed tunnel, network access, static policy
Implementation pitfalls and how to avoid them
- Pitfall: Overly broad access rules
- Solution: Start with least privilege, expand gradually through a controlled rollout.
- Pitfall: Inadequate posture checks
- Solution: Define clear posture baselines and enforce them consistently.
- Pitfall: Fragmented policy management
- Solution: Use a centralized policy engine to ensure consistency across ZIA, ZPA, and other security controls.
- Pitfall: User resistance and friction
- Solution: Communicate changes, provide easy onboarding, and ensure MFA is reliable and fast.
- Pitfall: Data privacy concerns
- Solution: Ensure logs and telemetry are compliant with privacy regulations; anonymize where possible.
Real-world technical tips
- Start with a pilot group that includes remote workers, contractors, and IT staff to validate policy clarity.
- Use SSO with MFA to reduce password fatigue and strengthen authentication.
- Integrate with your existing SIEM and SOAR for better incident response.
- Design for disaster recovery with multiple regional points of presence to minimize outages.
FAQ Section
Frequently Asked Questions
What is Zscaler and how does it relate to VPNs?
Zscaler is a cloud-based security platform offering secure access to apps ZPA and web traffic ZIA with zero-trust principles, reducing reliance on traditional VPN tunnels and improving app-level security.
How does zero trust differ from traditional VPN security?
Zero trust validates every access request based on user identity, device health, and context rather than automatically trusting devices inside the network perimeter.
Can ZPA replace all VPNs for remote workers?
For many organizations, ZPA can replace traditional VPNs for private app access, but the decision depends on your app portfolio and integration needs.
How does device posture impact access?
Device posture checks ensure only compliant, secure devices can access apps. Non-compliant devices may be denied or restricted until remediation is complete.
What is ZIA used for?
ZIA provides cloud-based secure web gateway capabilities, including URL filtering, malware protection, and data loss prevention for internet-bound traffic. Windscribe vpn extension for microsoft edge your ultimate guide in 2026
How do you integrate Zscaler with Active Directory or other IdPs?
You typically configure SSO with an IdP like Okta or Azure AD and sync user attributes to enforce policies and MFA across ZIA and ZPA.
Is MFA required for every access request?
MFA is strongly recommended for authentication, but policy can vary. Zero-trust architectures often require MFA for sensitive apps or unusual access patterns.
What about data residency and privacy?
Cloud-based security platforms can be configured to meet data residency requirements, and logs can be managed to comply with privacy laws.
How do I measure success after deployment?
Track time-to-access reduction, user friction metrics, security incidents, and policy accuracy. Look at SLA adherence for app access and incident response times.
How do I plan a rollout for multi-region teams?
Start with a regional deployment that covers the majority of users, then expand to other regions while adjusting policies for regional differences. Globalconnect vpn wont connect heres how to fix it fast: Quick Fixes, Tips, and Expert Hacks for Seamless VPN Access
What is the typical cost model for Zscaler-like architectures?
Costs usually include per-user or per-GB data usage, with tiered options for ZIA and ZPA services, plus potential costs for IdP and integration work.
How do I handle exceptions and break-glass access?
Define an explicit process for exceptions, including time-bound access, audit trails, and automatic revocation when the exception ends.
Can I run a hybrid approach with some VPNs still in place?
Yes, many organizations run a phased approach, retiring VPNs gradually as confidence and coverage with ZPA and ZIA grow.
How do I migrate users and data with minimal downtime?
Plan a migration window, run a parallel mode during initial rollout, and use phased cutovers with clear rollback plans.
What performance considerations should I expect?
Edge-based inspection, cloud routing, and policy checks may introduce small latency changes, but most users see improved performance due to local breakouts and fast app access. Microsoft edge tiene vpn integrada como activarla y sus limites en 2026: Guia completa, beneficios, limites y alternativas
How do I ensure compliance during a transition?
Implement logs, centralized policy repositories, and continuous auditing for access controls and data handling.
End of Frequently Asked Questions
Additional Resources
- Zscaler Official Documentation - zscaler.com
- Zero Trust Security Model Overview - en.wikipedia.org/wiki/Zero_trust_security_model
- Identity Providers Comparison - searchcatalog.example/idp-comparison
- Cloud Security Alliance Best Practices - cloudsecurityalliance.org
- Secure Web Gateway Best Practices - csoonline.com/secure-web-gateway
- Data Privacy and Compliance Guides - gdpr.eu, osha.gov, nist.gov
Notes
- This content is designed for educational purposes related to the topic of Zscaler and VPNs with a focus on secure access beyond traditional tunnels.
- For more detailed guidance, consult your security architect and use provider-specific deployment guides.
If you’d like, I can tailor this further to your target audience, add a downloadable checklist, or produce a YouTube-style script with sections and timestamps. How To Configure Intune Per App VPN For iOS Devices Seamlessly: Quick Setup, Best Practices, And Troubleshooting
Sources:
The ultimate guide best vpn for your ugreen nas in 2025
Big ip edge client vpn setup and troubleshooting guide for BIG-IP Edge Client VPN on Windows macOS Linux iOS Android 2026
Why Your itvx Isn’t Working With Your VPN and How to Fix It
Longevity Burn-In Investigative Paths After 3 Months: QD-OLED vs. WOLED, LG vs. Sony, And More 2026